The recent hack of the consumer credit reporting agency Equifax didn’t just expose the private information of up to 143 million Americans — it also exposed the need for a replacement to the current method in which Americans prove their identity.
Every American citizen has a Social Security number that is unique to them, which has naturally become the favored method for the government and for businesses to verify our identities. But that was never its intended use.
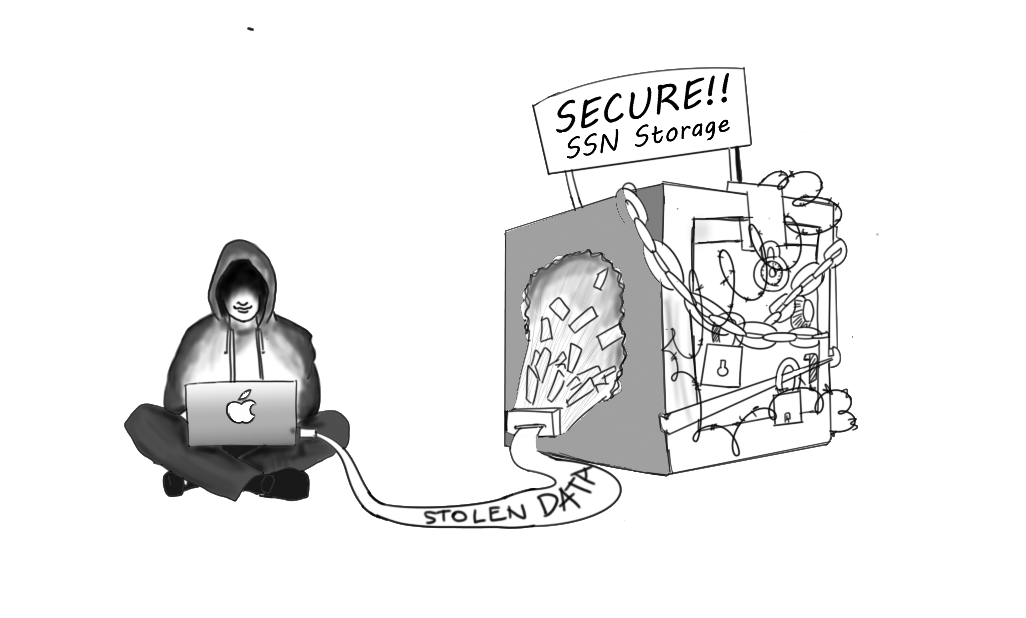
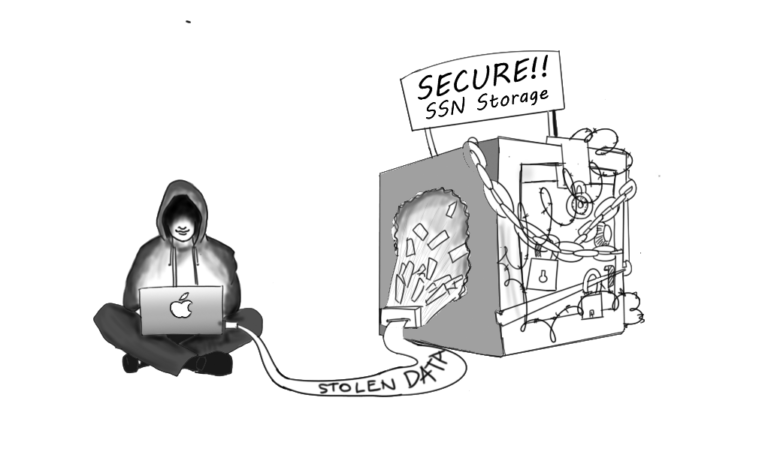
Social Security numbers are designed for one purpose: to keep track of a person’s lifetime earnings and years worked in order to calculate their Social Security payout when they reach the age of eligibility. The number is short and not completely random, so using one’s Social Security number as a form of identification was never secure. Nowadays, hackers can remotely breach a company’s servers and obtain the sensitive data of millions with little risk of being caught.
Many companies, recognizing the risk of digital attacks, put great efforts into keeping customer’s Social Security numbers secure. However, even the strongest security measures are rendered irrelevant by two factors.
First, larger companies tend to have stronger security, but they also tend to be more of a target for hacking. As the amount of personal data a company stores increases, so does the potential payout for stealing it. Because the incentive is so great, modern cyber security is less a question of if a company will be hacked and more a question of when.
Second, one’s Social Security is only as safe as its weakest holder. We are always told not to re-use our passwords on multiple sites, because if a hacker gets ahold of that one password, the can get access to all your sites. The way to stay secure is to use a different password for each site, yet, with Social Security numbers this is impossible.
Put simply, a Social Security number is a poor way to prove identity because it only works if the number is a secret, and nowadays, it’s impossible to keep it as such. The solution, then, is an identification system that need not be secretive. And such a system already exists in the form of one-time passwords (OTPs).
The number is short and not completely random, so using one’s Social Security number as a form of identification was never secure.
If you’ve ever had to verify an online account by entering in a code you received as a text message, you’ve already encountered a OTP. It is essentially a key that can only unlock a door once. Every time you sign into the account, you get a new password sent to you — a new key to unlock the door. Because OTPs can only be used once, it doesn’t matter if someone hacks in and steals it, because it no longer grants access your account.
But even more secure and convenient than receiving your one-time passwords via text message, you can receive them via an app on your phone that generates a new code every minute or so. When you need to sign in, the site prompts you to enter the code currently displayed in the app. Just like with the other system, the code can only be used once, and unlike the messaging method, even if your phone number is hacked, you are still safe.
So, when it comes to identification, why not replace the Social Security number with one-time passwords? A Social Security number is a popular way to identify people because it is universal and unique , but OTPs are both those things. They are universal because virtually everyone has a cell phone and therefore can have their own code generator. They are unique because everyone’s code generator creates different codes.
But most importantly, unlike Social Security numbers, they are secure. An OTP could be stolen or an account could be hacked, but because codes expire and cannot be reused, the hackers are left unable to access any other accounts.
The switch to OTPs could be an opt-in program. But given that, for the 143 million people whose Social Security numbers may no longer be a secret, the decision of whether or not to make the change would likely be any easy one.